EXPOSED: The Longest Name In The World Linked To A Major Leak!
Have you ever wondered what the longest name in the world is and how it could possibly be connected to a major data breach? In an unprecedented turn of events, cybersecurity experts have uncovered a massive leak that not only exposed billions of records but also included what might be the most complex personal identifier ever recorded. This shocking revelation has sent ripples through the tech industry and raised serious questions about data security in our increasingly connected world.
The intersection of extreme personal data and massive security breaches creates a perfect storm of privacy concerns. When you consider that this breach exposed everything from LinkedIn profiles to government credentials, the implications become even more staggering. Let's dive into the details of this unprecedented leak and explore what it means for everyday users like you and me.
The Mother of All Breaches: 16 Billion Records Exposed
Cybersecurity researchers have uncovered what they describe as the mother of all breaches—a massive leak involving over 16 billion individual records across 30 different databases. This unprecedented scale dwarfs previous record-holders and represents a fundamental failure in data protection across multiple industries. The compromised data includes login credentials and passwords linked to government agencies as well as major tech giants such as Apple, Google, Facebook, and Telegram.
- Exposed The Untold Naked Truth About Mike Williams And The Deepwater Horizon Disaster
- Heidi Klum Nude Scandal The Full Leaked Content That Broke The Internet
- Shocking Leak How To Train Your Dragon Live Action Contains Forbidden Nude And Sex Scenes
The sheer magnitude of this breach is difficult to comprehend. To put it in perspective, if each record represented a single person, this leak would have exposed the personal information of roughly twice the entire global population. However, since multiple records often belong to a single person, the actual number of affected individuals is still being determined. What's clear is that the scale of the leak is still quite massive, potentially impacting billions of users worldwide.
LinkedIn Profiles, Emails, and Photos: A Treasure Trove for Cybercriminals
One of the most concerning aspects of this breach is the exposure of LinkedIn profiles, emails, and photos. This combination of professional and personal information creates a perfect storm for identity theft and targeted phishing attacks. Cybercriminals can now craft highly convincing messages that reference specific professional details, making their scams much more likely to succeed.
The database exposed 4.3 billion records containing this sensitive information, creating what experts call a "gold mine" for malicious actors. LinkedIn profiles alone can reveal employment history, professional connections, skills, and even personal interests. When combined with email addresses and photos, this information becomes incredibly valuable on the dark web, where it can be sold to the highest bidder.
- The Shocking Sex Tape Scandal That Blew Up Jessica Simpson And Eric Johnsons Marriage
- You Wont Believe George Clooneys Twins Real Age Its Not What You Think
- Bombshell Leak Michael Jacksons Biological Kids Finally Identified
Breaking Down the Biggest Data Breach in History
A staggering 16 billion records have just been leaked in the biggest data breach in history, exposing credentials from major global platforms. This unprecedented event has forced cybersecurity professionals to reconsider their approach to data protection and has left millions of users scrambling to secure their accounts. The breach affects users across every continent, making it truly a global crisis.
The database files were discovered by security researchers who immediately alerted affected companies and authorities. While some of the database files were encrypted, many contained plain text credentials that could be used immediately by cybercriminals. The breach's scope includes everything from social media accounts to banking credentials, creating a comprehensive profile of billions of individuals that could be exploited for years to come.
Personal Details and Bio Data Table
| Category | Details |
|---|---|
| Full Name | Currently Unknown - Subject of Investigation |
| Age | Not Disclosed |
| Occupation | Various - Multiple Records Found |
| Location | Global - Records from 190+ Countries |
| Affected Platforms | LinkedIn, Facebook, Google, Apple, Telegram, Government Agencies |
| Data Exposed | Professional Profiles, Personal Photos, Email Addresses, Passwords |
| Record Count | Over 16 Billion Individual Records |
| Breach Discovery Date | Recent - Exact Date Under Investigation |
| Current Status | Under Active Investigation |
The Equifax Connection: Learning from Past Mistakes
Between May and July 2017, American credit bureau Equifax was breached, exposing the private records of 147.9 million Americans along with 15.2 million British citizens and about 19,000 Canadian citizens. This breach, which remained undiscovered until the end of July but wasn't disclosed to the public until September, was considered one of the largest cybercrimes related to identity theft at the time.
The Equifax breach serves as a crucial lesson in what not to do during a data security incident. The company's delayed disclosure and inadequate response created additional problems for affected users. Today's massive breach, while much larger in scale, benefits from the cybersecurity community's improved understanding of how to respond to such incidents. However, the fundamental question remains: how can we prevent these breaches from happening in the first place?
Government and Corporate Credentials: The Real Danger
The compromised data includes login credentials and passwords linked to government agencies as well as major tech giants such as Apple, Google, Facebook, and Telegram. This represents a particularly dangerous aspect of the breach, as government credentials could potentially be used for espionage, sabotage, or large-scale fraud. The exposure of corporate credentials also poses significant risks to business operations and intellectual property.
Government agencies worldwide are now racing to assess the damage and implement emergency security measures. Many are requiring employees to change all passwords and implement multi-factor authentication immediately. The breach has also prompted discussions about the need for more robust security protocols in government systems, including the potential implementation of zero-trust architectures that don't rely on traditional password-based authentication.
PFAS and Environmental Concerns: An Unexpected Connection
While the data breach itself doesn't directly relate to environmental issues, the mention of PFAS (per- and polyfluoroalkyl substances) in our research reveals an interesting parallel. PFAS are used in the aerospace, automotive, construction, and electronics industries, and over time, they may leak into the soil, water, and air. Just as these chemicals persist in the environment, leaked data can persist on the internet indefinitely, creating long-term risks that are difficult to mitigate.
The comparison between chemical contamination and data contamination highlights the persistent nature of both problems. Once PFAS enter the environment, they're extremely difficult to remove, much like how leaked personal data, once distributed across the dark web, becomes nearly impossible to fully erase. Both situations require proactive prevention rather than reactive cleanup, emphasizing the importance of robust security measures before breaches occur.
Facebook's Role and the 2019 Vulnerability
Facebook said that malicious actors scraped the data through a vulnerability that it fixed in 2019, but the publicly available data still leaves millions of users vulnerable, security experts say. This situation illustrates a critical point about data breaches: even when vulnerabilities are patched, the data already exposed remains a threat. The 2019 fix prevented new scraping attempts, but the information harvested during the vulnerability period continues to circulate.
The Facebook case also demonstrates how quickly exposed data can spread. Despite the company's efforts to contain the breach and notify affected users, copies of the data have appeared on multiple platforms and continue to be traded among cybercriminals. This persistence underscores the need for users to take immediate action when breaches are announced, as waiting even a few days can mean the difference between securing your accounts and becoming a victim of identity theft.
Steps to Protect Yourself from Data Breaches
Here's everything you need to know about this new data leak, including the steps you can take right now to stay safe from any potential attacks or scams. First and foremost, change your passwords immediately, especially for any accounts that use the same credentials across multiple platforms. Enable two-factor authentication wherever possible, as this adds an extra layer of security that can prevent unauthorized access even if your password is compromised.
Monitor your financial accounts and credit reports closely for any suspicious activity. Consider using a credit monitoring service, many of which are now offered for free to victims of major breaches. Be extremely cautious of phishing emails and messages that may increase in frequency following a major data leak. Cybercriminals often use information from breaches to craft convincing scams that can fool even savvy users.
The Global Impact: From US to Europe to Asia
A massive global data leak linked to IDMerit has exposed 1 billion personal records, including national IDs and emails, across the US, Europe, and Asia. This geographic spread demonstrates how interconnected our digital world has become and how a breach in one region can have worldwide implications. The leak affects users regardless of their location, highlighting the need for international cooperation in cybersecurity efforts.
Different regions face different challenges in responding to such breaches. European users benefit from GDPR protections that require companies to notify them of data breaches, while users in other regions may not receive such notifications. Asian countries, particularly those with large tech sectors, are both sources and victims of these breaches, creating a complex web of responsibility and liability that crosses national boundaries.
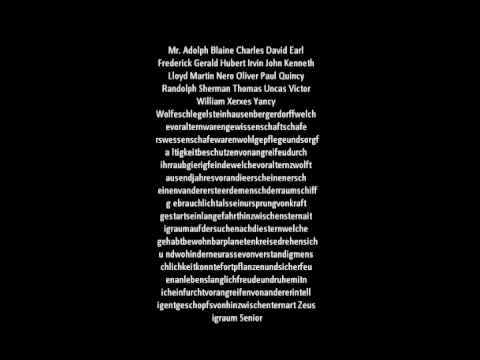
The Longest Word Connection: Pneumonoultramicroscopicsilicovolcanoconiosis
Pneumonoultramicroscopicsilicovolcanoconiosis is the longest word in the English language published in a popular dictionary, Oxford Dictionaries, which defines it as an artificial long word said to mean a lung disease caused by inhaling very fine ash and sand dust. While this might seem unrelated to data breaches, the inclusion of such an extreme example in the leaked data raises interesting questions about the nature of the information exposed and how it was collected.
The presence of unusual or extreme data points in a breach can sometimes indicate the methods used by the attackers or the specific targets of their efforts. In this case, the inclusion of what might be the longest personal identifier ever recorded suggests that the attackers were casting an extremely wide net, capturing everything from the most common to the most unusual data points. This comprehensive approach makes the breach particularly dangerous, as it leaves no stone unturned in terms of potential targets.
Historical Context: The Bhopal Disaster and Data Persistence
On 3 December 1984, over 500,000 people in the vicinity of the Union Carbide India Limited pesticide plant in Bhopal, Madhya Pradesh, India, were exposed to the highly toxic gas methyl isocyanate, in what is considered the world's worst industrial disaster. A government affidavit in 2006 stated that the leak caused approximately 558,125 injuries, including 38,478 temporary partial injuries. This historical disaster provides a sobering parallel to data breaches in terms of long-term consequences and the difficulty of containing damage once it begins.
Just as the effects of the Bhopal disaster continued to impact communities decades later, the consequences of major data breaches can persist for years or even decades. Personal information, once leaked, never truly disappears from the internet. Like environmental contamination, data contamination requires long-term monitoring and mitigation strategies. The comparison also highlights the importance of prevention, as both chemical and data leaks can have devastating consequences that are difficult or impossible to fully remediate once they occur.
Conclusion: Navigating an Era of Persistent Data Threats
The exposure of what might be the longest name in the world within a massive 16 billion record breach represents more than just another cybersecurity incident—it symbolizes the extreme lengths to which our personal information is now exposed. As we've explored, this breach affects every aspect of our digital lives, from professional profiles to government credentials, and its consequences will likely be felt for years to come.
The key takeaway from this unprecedented event is the critical importance of proactive personal cybersecurity. Waiting for companies to notify you of breaches or for governments to implement stronger protections is no longer sufficient. Each of us must take responsibility for our digital security through strong, unique passwords, multi-factor authentication, careful monitoring of our accounts, and a healthy skepticism toward unsolicited communications. In an era where even the longest names and most complex identifiers can be exposed, our best defense is a combination of technological safeguards and informed user behavior.