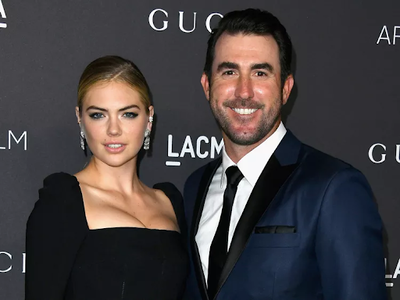
Kate Upton's Scandalous Leak Leaves Justin Verlander In Emotional Ruins!
In September 2014, the world watched in shock as intimate photos of model Kate Upton and Detroit Tigers pitcher Justin Verlander were leaked online, sparking a massive celebrity hacking scandal that would leave both their relationship and personal lives in turmoil. How could such a devastating breach of privacy happen to two high-profile celebrities, and what were the long-term consequences of this digital invasion?
This scandal not only exposed the vulnerability of celebrities in the digital age but also raised serious questions about online security, privacy rights, and the ethics of consuming leaked intimate content. Let's dive deep into this controversial incident and explore its far-reaching impact on both Kate Upton and Justin Verlander.
Biography of Kate Upton
Kate Upton, born Katherine Elizabeth Upton on June 10, 1992, in St. Joseph, Michigan, is an American model and actress who rose to fame through her appearances in the Sports Illustrated Swimsuit Issue. Her journey from a small-town girl to an international supermodel is nothing short of remarkable.
- Epsteins Final Leak Disturbing Details Of His Porn Ring And Leslie Wexners Role Revealed
- Sex Scandal Bombshell Sweet Home Alabama Stars Secret Affairs Revealed
- You Wont Believe What Just Leaked Epsteins Shocking Sex Tapes From Netflix Doc
Personal Details
| Detail | Information |
|---|---|
| Full Name | Katherine Elizabeth Upton |
| Date of Birth | June 10, 1992 |
| Place of Birth | St. Joseph, Michigan, USA |
| Height | 5'10" (178 cm) |
| Occupation | Model, Actress |
| Years Active | 2008 - Present |
| Notable Work | Sports Illustrated Swimsuit Issue, The Other Woman |
| Partner | Justin Verlander (married in 2017) |
The 2014 Scandal: How It Unfolded
The scandal broke in late August 2014 when hundreds of nude photos of celebrities, including Kate Upton and Justin Verlander, were illegally leaked to the internet. This massive hacking incident, later dubbed "The Fappening," sent shockwaves through Hollywood and beyond.
The Initial Leak
On August 31, 2014, an anonymous user posted a collection of private photos on the imageboard 4chan, claiming they had been obtained through a breach of iCloud accounts. Among the leaked images were intimate photos of Kate Upton and Justin Verlander, which quickly spread across the internet like wildfire.
The timing couldn't have been worse for the couple. Just days before the leak, they had attended an NBA game together, appearing happy and in love. Little did they know that their private moments were about to be exposed to the world in the most humiliating way possible.
- Shocking Leak How To Train Your Dragon Live Action Contains Forbidden Nude And Sex Scenes
- How Ice Spice Lost 50 Pounds Overnight Nude Photos Reveal The Method
- Emotional Breakdown Call The Midwife Stars Confess Hidden Truths That Will Make You Cry
The Scope of the Breach
The hacking scandal affected dozens of high-profile celebrities, including Jennifer Lawrence, Kirsten Dunst, and Ariana Grande. However, the inclusion of Justin Verlander, a professional athlete, made this breach particularly noteworthy as it crossed into the sports world.
Key details of the breach:
- Over 500 private photos were leaked
- The hack affected celebrities from various industries
- Apple's iCloud service was identified as the primary vulnerability
- The incident sparked a global conversation about digital privacy and security
How the Hack Happened: Understanding the Security Breach
The 2014 celebrity photo leak wasn't just a random act of hacking; it was a sophisticated operation that exploited weaknesses in cloud storage security.
The Phishing Scam
According to cybersecurity experts, the hackers used a combination of social engineering and technical exploits to gain access to the victims' accounts. The primary method was phishing scams targeting iCloud and Gmail accounts.
How the phishing worked:
- Hackers sent emails that appeared to be from legitimate services like Apple or Google
- These emails contained links to fake login pages
- Unsuspecting users entered their credentials, which were then captured by the hackers
- With these credentials, hackers could access not only email accounts but also connected cloud storage services
Apple's Response
Apple initially denied that their systems had been breached, stating that the incident was the result of targeted attacks on user names, passwords, and security questions. However, the company did acknowledge weaknesses in its security protocols and took steps to improve them.
Security improvements implemented by Apple:
- Introduction of two-factor authentication
- Enhanced security questions
- Improved account recovery processes
- Better monitoring of suspicious login attempts
Justin Verlander's Response: Breaking His Silence
In the aftermath of the leak, Justin Verlander, known for his typically private nature, found himself thrust into an unwanted spotlight. The Detroit Tigers' star pitcher initially declined to comment on the situation, but eventually broke his silence.
First Public Statement
On Tuesday, September 2, 2014, Verlander addressed the media for the first time since the photos surfaced. His statement was brief but telling: "I want to keep my private life just that — private."
This simple declaration spoke volumes about the emotional toll the incident had taken on him. As a professional athlete, Verlander was used to scrutiny on the field, but this invasion of his personal life was an entirely different matter.
Impact on His Career
While the scandal didn't directly affect Verlander's performance on the field, it undoubtedly created additional stress and distraction. The Detroit Tigers were in the midst of a crucial season, and Verlander had to navigate both his professional responsibilities and the personal trauma of having his privacy violated.
Kate Upton's Legal Action and Public Response
Kate Upton, known for her outspoken personality, took a more aggressive stance in response to the leak. She immediately vowed legal action against those responsible for the hack and the distribution of the photos.
Legal Strategy
Upton's legal team focused on several key areas:
- Identifying and prosecuting the hackers
- Pursuing civil action against websites hosting the content
- Advocating for stronger privacy laws
- Raising awareness about digital security
Public Support and Backlash
The incident sparked a heated debate about privacy rights and victim blaming. While many supported Upton and the other victims, some critics unfairly suggested that celebrities should expect such breaches as part of their public lives.
Upton's powerful statement:
"My family and I are not the only victims of this crime. There are hundreds of victims. And we need to come together and fight back."
Lessons Learned from the Celebrity Photo Leak
The 2014 hacking scandal taught us several important lessons about digital security and privacy in the modern age.
1. The Importance of Strong Passwords
One of the most crucial takeaways from this incident was the need for robust password security. Many of the hacked accounts were compromised due to weak or reused passwords.
Best practices for password security:
- Use unique passwords for each account
- Implement a password manager
- Create complex passwords with a mix of characters
- Regularly update passwords
2. Two-Factor Authentication is Essential
The scandal highlighted the importance of two-factor authentication (2FA) in protecting online accounts. This additional layer of security could have prevented many of the breaches.
How 2FA works:
- Enter your password as usual
- Receive a code via text or authentication app
- Enter the code to complete login
- Even if someone has your password, they can't access your account without the second factor
3. Cloud Storage Security Awareness
The incident raised awareness about the potential vulnerabilities of cloud storage services. Users became more cautious about what they stored in the cloud and how they protected their accounts.
Tips for safer cloud storage:
- Be selective about what you store in the cloud
- Use encryption for sensitive files
- Regularly review and clean up cloud storage
- Understand the privacy policies of your cloud service provider
4. The Ethics of Consuming Leaked Content
The scandal sparked an important conversation about the ethics of viewing and sharing leaked intimate content. It raised questions about digital consent and the responsibility of internet users.
Ethical considerations:
- Respecting others' privacy
- Understanding the harm caused by sharing intimate content without consent
- Recognizing the human impact behind leaked photos
- Reporting rather than sharing leaked content
The FBI Investigation and Legal Consequences
The scale and nature of the hack prompted a full-scale investigation by the FBI, highlighting the seriousness of the crime.
The Investigation Process
The FBI's investigation, codenamed "Operation No Tricks, No Treats," involved:
- Tracing the digital footprints of the hackers
- Collaborating with international law enforcement agencies
- Working with tech companies to identify vulnerabilities
- Gathering evidence for prosecution
Legal Outcomes
While several individuals were eventually arrested and prosecuted in connection with the hack, the case also led to broader legal discussions about digital privacy and cybercrime.
Notable legal developments:
- Increased penalties for hacking and privacy violations
- New legislation proposed to protect against digital exploitation
- Greater cooperation between tech companies and law enforcement
- Enhanced international agreements on cybercrime prosecution
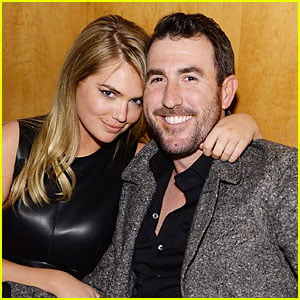
The Long-Term Impact on Upton and Verlander's Relationship
The scandal undoubtedly put a strain on Kate Upton and Justin Verlander's relationship, but it also revealed the strength of their bond.
Navigating the Aftermath Together
In the months and years following the leak, Upton and Verlander were often seen supporting each other publicly. Their united front in the face of adversity seemed to strengthen their relationship.
Public appearances post-scandal:
- Red carpet events where they appeared more protective of each other
- Joint interviews where they discussed the importance of privacy
- Social media posts showing their continued support and love
From Scandal to Marriage
In a surprising turn of events, Upton and Verlander got engaged in 2016 and married in 2017. Their ability to weather this storm and build a life together speaks to their resilience and commitment to each other.
The Broader Impact on Celebrity Culture and Privacy
The 2014 hacking scandal had far-reaching effects on how celebrities approach their digital lives and public personas.
Changes in Celebrity Behavior
In the wake of the scandal, many celebrities became more cautious about their digital footprint:
- Increased use of secure messaging apps
- Greater awareness of cloud storage risks
- More guarded approach to sharing personal information online
- Investment in personal cybersecurity measures
Industry-Wide Security Improvements
The incident prompted tech companies to reevaluate and strengthen their security measures:
- Enhanced encryption protocols
- Improved user authentication methods
- Better monitoring of suspicious activities
- More transparent communication about security breaches
Conclusion: Lessons for the Digital Age
The 2014 celebrity photo leak scandal involving Kate Upton and Justin Verlander was more than just a shocking invasion of privacy; it was a wake-up call for the digital age. It exposed the vulnerabilities in our online lives and sparked important conversations about privacy, security, and ethics in the digital realm.
As we move forward, the lessons learned from this incident continue to shape how we approach online security and digital privacy. For celebrities and everyday users alike, it serves as a reminder of the importance of protecting our digital identities and respecting the privacy of others.
The resilience shown by Upton and Verlander in the face of this crisis is commendable, but it also highlights the ongoing challenges we all face in maintaining privacy in an increasingly connected world. As technology continues to evolve, so too must our approach to digital security and our understanding of privacy rights.
In the end, the scandal that left Justin Verlander and Kate Upton's lives in emotional ruins also paved the way for important changes in how we view and protect our digital selves. It's a reminder that in the age of information, our greatest asset – and our greatest vulnerability – is the data we create and share.